Executive Summary
The modern counterfeit supply chain is no longer limited to hidden warehouses and physical storefronts. Today, bad actors exploit highly fragmented digital networks utilizing social commerce, cross platform dropshipping, and influencer marketing to distribute illicit goods globally. As these operations become increasingly decentralized, traditional manual enforcement falls short. Brand protection now requires deploying specialized AI agents capable of analyzing deep data points across multiple platforms to expose hidden networks, neutralize influencer driven fraud, and protect brand integrity at the source.
--
The Evolution of Illicit Logistics
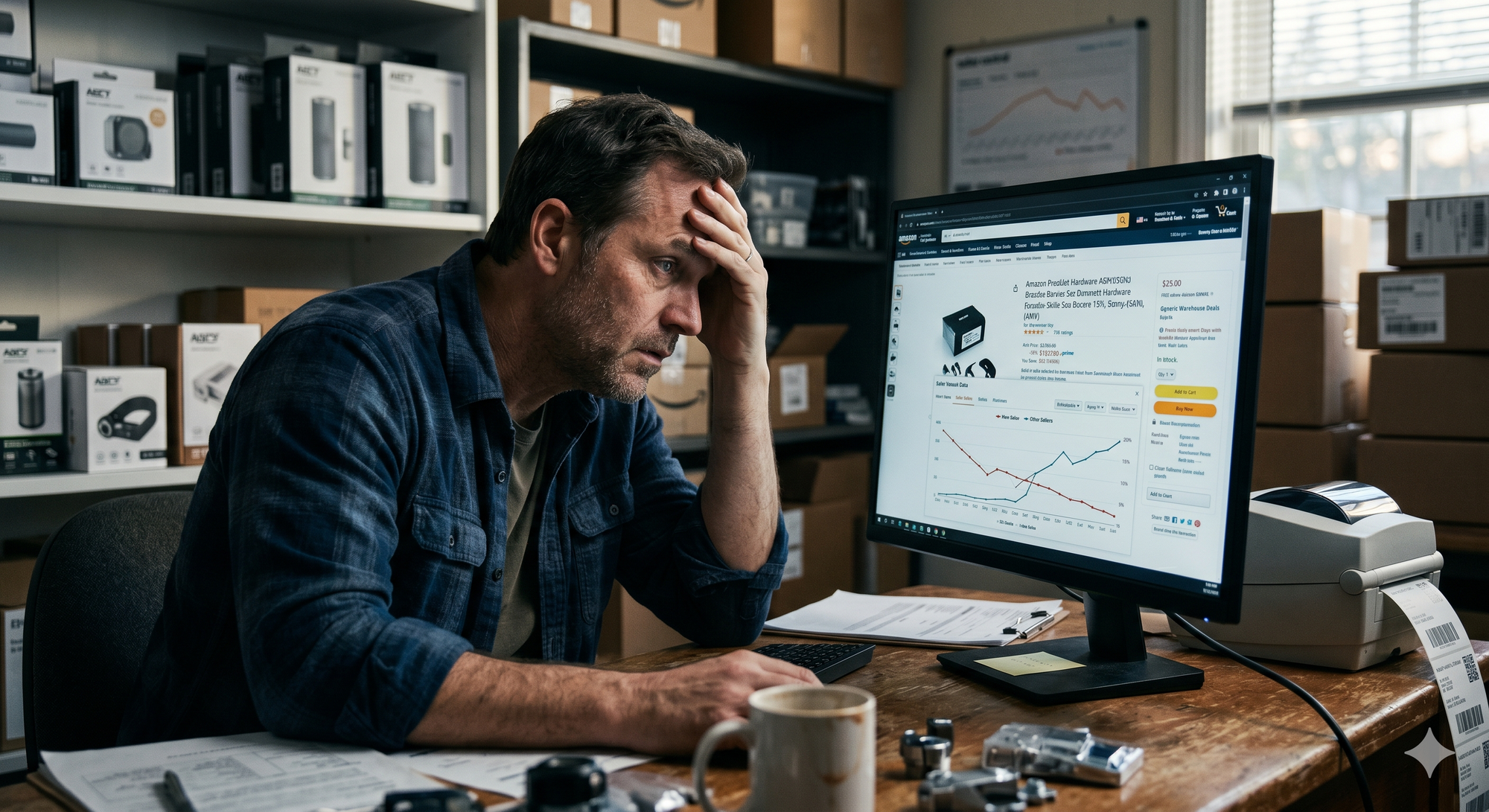
The architecture of counterfeit distribution has undergone a massive transformation. Historically, identifying a counterfeit ring meant tracking large freight shipments and raiding physical markets. Today, the supply chain is entirely digitized and decentralized. Counterfeiters operate fluidly across digital marketplaces and social media platforms, shipping single items directly to consumers to evade customs detection.
This digital shift has given rise to the phenomenon of "social commerce risks." Bad actors create multiple disposable storefronts across various regions. When one account is flagged, they simply pivot to another pre established profile. Counterfake provides advanced AI supported solutions against this type of digital fraud and counterfeiting to help businesses protect their brand value and customer trust. Because fake products are sold across e-commerce platforms, social media, and individual marketplaces, continuous and automated monitoring is essential.
The Role of Influencer Marketing Fraud
A critical node in this new supply chain is the exploitation of influencer marketing. Counterfeit networks frequently collaborate with micro influencers to promote "dupes" or high quality unauthorized replicas. These influencers act as the marketing arm of the illicit supply chain, directing high intent buyers to cross listed products on secondary marketplaces.
These campaigns are designed to look authentic. The visual content often features real lifestyle imagery, making it difficult for standard detection algorithms to flag the content as fraudulent. To combat this, brand enforcement strategies must look beyond simple keyword matching and analyze the entire context of the promotion.
Dismantling the Network with Specialized AI
To effectively disrupt these modern supply chains, brands need a solution that mimics the complexity of the networks themselves. Counterfake utilizes a suite of Specialized AI Agents that analyze products, images, sellers, and reviews across platforms with a proven 95% success rate.
Here is how the technology targets the nodes of the counterfeit supply chain:
- Mapping the Seller Network: The Seller Agent evaluates seller reliability, unverified contact info, and counterfeit history. By integrating Deep Search and Insight Analysis, the system detects identical listings across different platforms and flags risky sellers using comprehensive image and price comparisons. This reveals the hidden links between seemingly unrelated seller accounts.
- Visual and Structural Verification: Counterfeiters often use stolen or manipulated images. The Image Agent analyzes product photos with AI to detect anomalies in logos, shapes, and pricing signals. Furthermore, Shape Detection compares product contours and proportions to find physical mismatches with originals, such as a contour mismatch in a toe area.
- Brand and Logo Auditing: The system performs rigorous Brand and Design Detection to check design patterns, colors, and trademarks for unauthorized variations. Logo Detection specifically identifies trademarked logos and detects potential brand confusion or misuse with high confidence.
- Contextual Intelligence: The Comment Agent conducts review and rating analysis to spot coordinated fake reviews , while the Platform Agent conducts platform security analysis to identify rule violations, including the sale of prohibited items.
Ultimately, the Counterfake AI Reasoning Model evaluates all agent data simultaneously to make the final, accurate counterfeit determination. This holistic approach is why major e-commerce platforms with millions of products trust Counterfake to combat fraud. It is also why Meta selected Counterfake for its global Llama Impact Grant as the only company from Turkey.
The reality of digital commerce is that as long as there is demand, illicit networks will continue to evolve their supply chains. However, these networks leave digital footprints. Every fake review, manipulated image, and unverified seller profile is a data point waiting to be analyzed. By deploying comprehensive AI brand protection software, companies can shift from playing a reactive game of takedowns to proactively mapping and dismantling the infrastructure of counterfeiters. Securing your brand's future requires securing the digital channels where your customers live, ensuring that every interaction remains authentic and safe.
References:
- OECD & EUIPO – "Global Trade in Fakes: A Worrying Threat" (Detailing the shift toward small parcel, digitized logistics in counterfeit distribution).
- Interpol – "Illicit Markets and Social Media: The New Frontier of Intellectual Property Crime" (Analyzing the role of social commerce platforms in facilitating global counterfeit networks).
- U.S. Patent and Trademark Office (USPTO) – "The Impact of E-commerce and Influencer Marketing on Brand Counterfeiting" (Exploring the intersection of influencer fraud and online brand enforcement).